Squid is a caching proxy for the Web supporting HTTP, HTTPS, FTP, and more.
Squid can be configured to make SSL/TLS inspection (aka HTTPS interception) so the proxy can decrypt proxied traffic (Squid calls this feature ssl bump).
Afaik the Squid package included in the Linux distros is not compiled with SSL/TLS inspection support but the good news is that diladele (its github repo and Websafety documentation are useful resources) provides packages for Ubuntu and Centos, recompiled (you can do by yourself) with support for HTTPS filtering and SSL/TLS inspection. This means that we have just to configure Squid. Not an easy task anyway 🙂
I provide to you a working config, follow next steps.
On Ubuntu 18.04 install diladele Squid 4.10 package with SSL support.
# required for apt-key
sudo apt-get update && sudo apt-get install -y gnupg wget
# add diladele apt key
wget -qO - http://packages.diladele.com/diladele_pub.asc | sudo apt-key add -
# add diladele repo
sudo echo "deb http://squid410.diladele.com/ubuntu/ bionic main" > /etc/apt/sources.list.d/squid410.diladele.com.list
# install squid 4.10 with SSL support
sudo apt-get update && sudo apt-get install -y \
squid-common \
squid \
squidclient \
libecap3 libecap3-devThen clone my github repo and make a symlink of the conf/ dir in /opt/.
# clone my repo
sudo apt-get install -y git
git clone https://github.com/gmellini/squidproxy-conf.git
# make a symlink in /opt/
cd squidproxy-conf
sudo ln -s ${PWD}/conf/ /opt/Start Squid.
# before we have to initialize SSL certificate database directory
sudo /usr/lib/squid/security_file_certgen -c -s /var/spool/squid_ssldb -M 4MB
# start Squid as a daemon
sudo /usr/sbin/squid -YC -N -f /opt/conf/squid/squid.conf
# OR in foreground
sudo /usr/sbin/squid -YC --foreground -f /opt/conf/squid/squid.confI also uploaded a docker container on dockerhub, grab and start it as follow.
# pull the container
sudo docker pull cybersaiyan/lab:squid
# run
sudo docker run -d --name SQUID -p3128:3128 cybersaiyan/lab:squid /usr/sbin/squid -YC --foreground -f /opt/conf/squid/squid.conf
# run and mount container log dir in host /tmp/log dir
mkdir /tmp/log && chmod 777 /tmp/log/
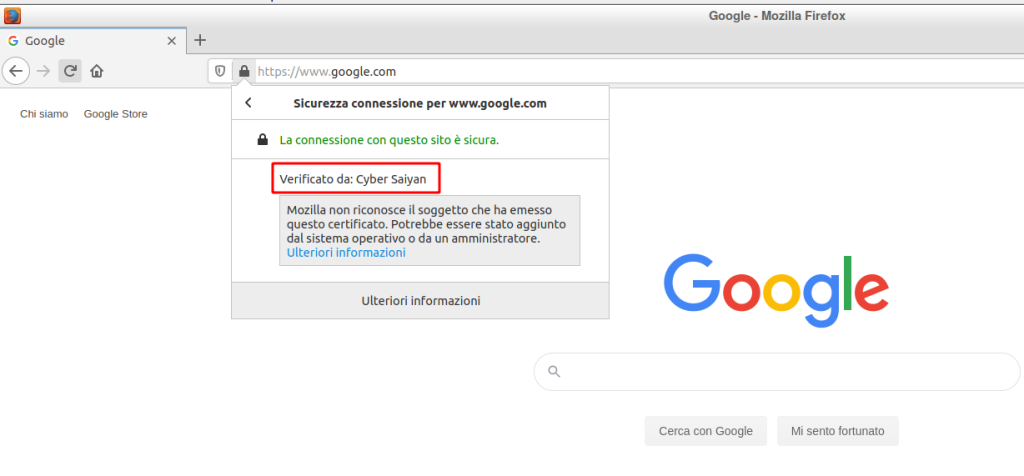
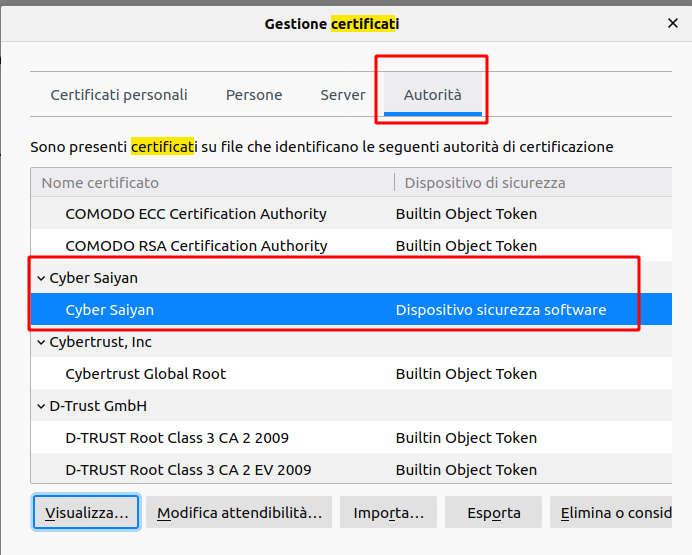
sudo docker run -d --name SQUID -p3128:3128 -v /tmp/log:/var/log/squid/ cybersaiyan/lab:squid /usr/sbin/squid -YC --foreground -f /opt/conf/squid/squid.confThen import X.509 Cyber Saiyan certificate in your browser Certificates/Autorities section; you can find the certificate in the local github conf/certs/ dir too or you can rebuild by yourself.
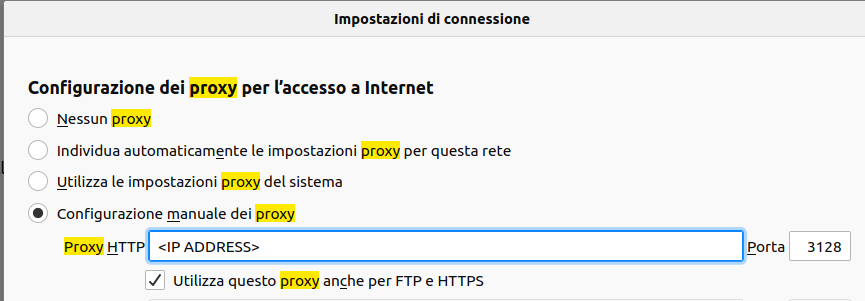
Set your browser HTTP proxy to <IP ADDRESS>:3128 for all protocols.
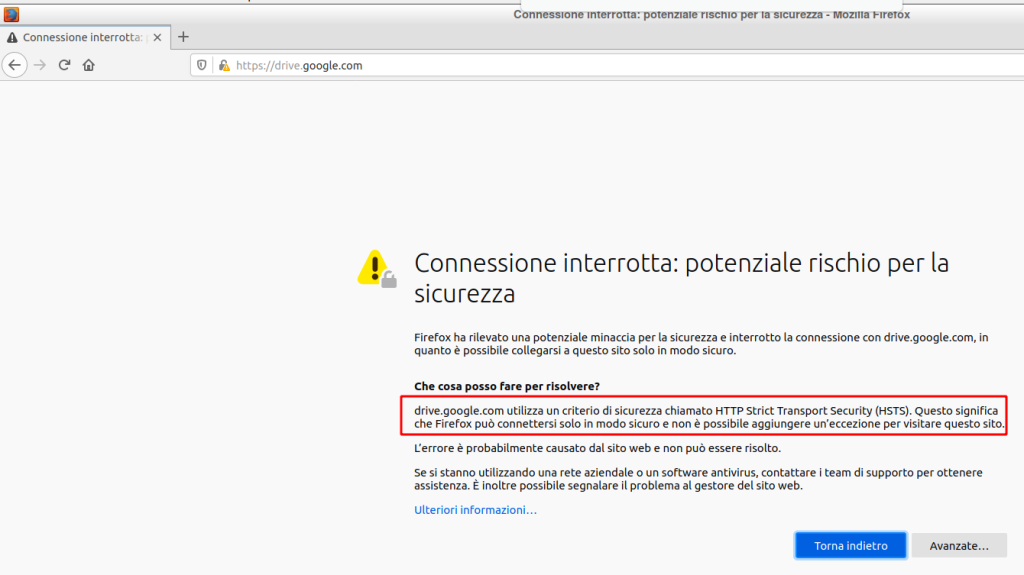
Start surfing some https web page; you can receive a certificate error, check at the end of the post why.
You will see the https web pages signed with Cyer Saiyan certificate and the good lock icon, this means a successfull SSL/TLS inspection.
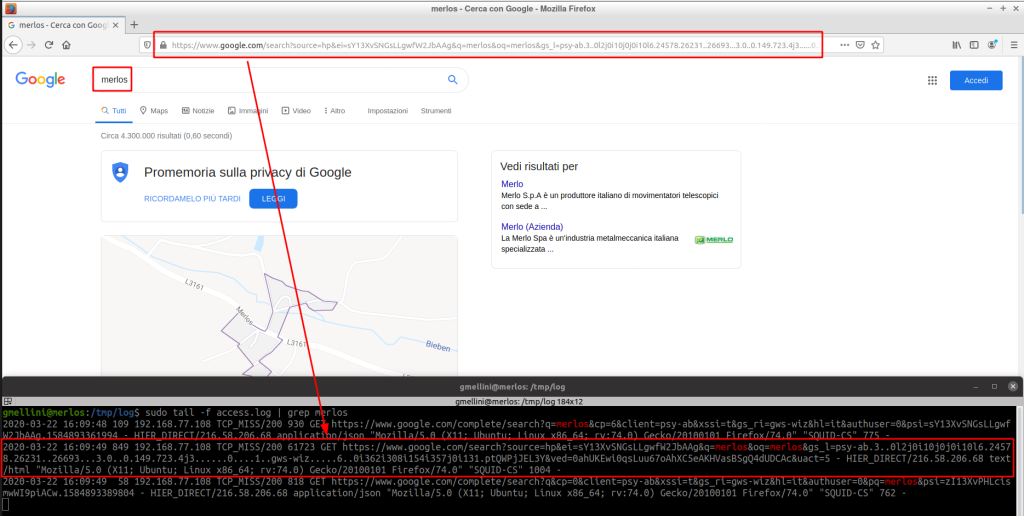
In the log dir – access.log file – you can check the connection logs; the log format is customized and is the same I use in my SOC.
You can whitelist websites on headers, ips, domains; telegram and whatsapp web chats are provided as an example. Each option of squid.conf file is commented with a link to the Squid web site.
Websites that implement HTTP STS headers and browsers with HSTS preloading feature can block bumping; look at drive.google.com error.
That’s it, enjoy.
Hi,
I am stuck at below
# before we have to initialize SSL certificate database directory
sudo /usr/lib/squid/security_file_certgen -c -s /var/spool/squid_ssldb -M 4MB
————————–
this gives an error
root@ubuntu3-VirtualBox:~/squidproxy-conf# sudo /usr/lib/squid/security_file_certgen -c -s /var/spool/squid_ssldb -M 4MB
sudo: /usr/lib/squid/security_file_certgen: command not found
I am new to both ubunty as well as squid proxy let alon ssl bumping.
Therefore I appreciate if you could let me know what I may be doing wrong here
Thanks,
Buddhika
LikeLike
security_file_certgen is included in squid 4.10 diladele package
Please be sure to install the needed packages before launch the command
LikeLike
Great Post!!
Can I use this for Debian10 setup? or what can I change so I can use it for Debian10?
LikeLike
Didn’t tried on Debian, probably will work on Debian too. If you try report back and I’ll update the post
tks
LikeLike
Can i see squid.conf file please…
LikeLike
squid configs (including squid.conf file) are in my github repo, linked in the post
https://github.com/gmellini/squidproxy-conf
LikeLike
I Cannot access http://squid410.diladele.com/ubuntu/ btw, is that different if i use http://squid413.diladele.com/ ??
LikeLike
squid413 is a package update from diladele. I didn’t tested (I will do and update the blog post, tks) but I think it will work, the squid config that I put in y github repo is pretty simple and standard, so 99% will work with diladele’s updated package
LikeLike
Thanks for your respond, i will waiting from your update
LikeLike